Privacy-preserving Communications
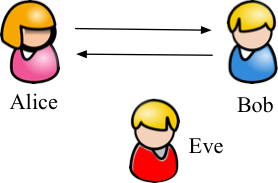 As our dependence on the rapidly expanding wireless ecosystem increases,
we are challenged with serious threats related to user privacy, data
confidentiality, and critical system availability. A significant portion
of these threats is attributed to the open wireless medium, which
exposes the system to passive and active attacks. Using commodity radio
hardware, unauthorized parties can easily eavesdrop on over-the-air
packet transmissions, without gaining physical access to secure
infrastructures. Eavesdropped packets can be analyzed to breach the
user’s privacy by tracking his whereabouts and movements, inferring his
associations, his wellbeing (medical conditions), and his preferences
(political, social, etc.). Moreover, they can be used to extract
intelligence for launching sophisticated active attacks.
As our dependence on the rapidly expanding wireless ecosystem increases,
we are challenged with serious threats related to user privacy, data
confidentiality, and critical system availability. A significant portion
of these threats is attributed to the open wireless medium, which
exposes the system to passive and active attacks. Using commodity radio
hardware, unauthorized parties can easily eavesdrop on over-the-air
packet transmissions, without gaining physical access to secure
infrastructures. Eavesdropped packets can be analyzed to breach the
user’s privacy by tracking his whereabouts and movements, inferring his
associations, his wellbeing (medical conditions), and his preferences
(political, social, etc.). Moreover, they can be used to extract
intelligence for launching sophisticated active attacks. We focus on designing and evaluating privacy-preserving communication methods for mitigating information leakage due to eavesdropping. Novel physical-layer obfuscation techniques that carefully control intentional interference from transmitters and/or receivers are being designed to prevent traffic analysis at the frame level. We further develop traffic normalization mechanisms at the flow level, whose objective is to hide complex network and traffic features, such as device role, routing paths, etc. Colluding eavesdroppers who monitor the system for long periods of time are also being investigated. Our methods strengthen the security, privacy, and usability of a wide range of critical systems that rely on wireless technologies, including transportation and aviation networks, mobile computing platforms, e-commerce, critical national infrastructures, medical systems, and others.
UA Engineering Research Aims to Secure Wi-Fi and Shut Out Snoops
Related Project
 NSF CNS-1409172: Leakage of Communications Signatures: Analysis of Eavesdropping Attacks and Proactive
Countermeasures - with Marwan Krunz (PI).
NSF CNS-1409172: Leakage of Communications Signatures: Analysis of Eavesdropping Attacks and Proactive
Countermeasures - with Marwan Krunz (PI).