NETVUE: Cybersecurity Visualization using Internet Maps
 Computer networks are constantly under attack. Adversaries regularly scan networks to look for vulnerable computers, launch Denial-of-Service (DoS) attacks, infect computers with malware (viruses, worms, and trojan horses), collect private information, and recruit computers into botnets that can be used to launch further attacks. To counter such malicious behavior, network security engineers constantly monitor their network for suspicious activities. This is a daunting task: not only is the data that has to be monitored enormous, but it is a cacophony of malicious and normal traffic originating from disparate sources. Given the volume and complexity of raw data, a well-integrated and well-designed visualization system can be used for effective presentation and interactive analysis of the underlying data.
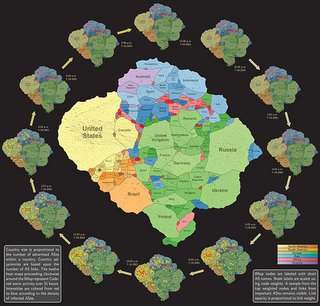
Computer networks are constantly under attack. Adversaries regularly scan networks to look for vulnerable computers, launch Denial-of-Service (DoS) attacks, infect computers with malware (viruses, worms, and trojan horses), collect private information, and recruit computers into botnets that can be used to launch further attacks. To counter such malicious behavior, network security engineers constantly monitor their network for suspicious activities. This is a daunting task: not only is the data that has to be monitored enormous, but it is a cacophony of malicious and normal traffic originating from disparate sources. Given the volume and complexity of raw data, a well-integrated and well-designed visualization system can be used for effective presentation and interactive analysis of the underlying data. As part of the Proactive Computer Network Defense and Information Assurance (CND/IA) Future Naval Capabilities (FNC) Program funded by the Office of Naval Research (ONR), we study visualization techniques for converting large-scale relational data into a geographic map metaphor. As people are familiar with the concept of geographical maps in day-to-day life, it is easier to use maps as a means to convey complex data in a meaningful form. We develop a system called NETVUE, which employs a unified metaphor – the geographic map – for visualizing network activity of interest. This map metaphor is not purely based on the geographic location of the input data; rather, it is a synthetic map that reflects the inherent relationships between the collected datasets. For example, a map could represent the global Internet topology, organized at different levels of granularity (e.g., at the autonomous system (AS) level, the Internet is made up of approximately 65,000 interconnected autonomous systems).
For more information about the project, please refer to: http://netviz.cs.arizona.edu/ and http://vizsec-gama.cs.arizona.edu/
UA Researchers Awarded $3.6M to Design Metaphorical Cybersecurity Map
Related Project
 ONR: Putting Network Security on the Map: Visualizing Network Security with a Unified Map Metaphor - with Stephen Kobourov (PI) and Christian Collberg (co-PI).
ONR: Putting Network Security on the Map: Visualizing Network Security with a Unified Map Metaphor - with Stephen Kobourov (PI) and Christian Collberg (co-PI).